Securing the Subscriber — Going Beyond the Gateway
By Steve Goeringer
Broadband is increasingly important in our lives. Broadband provides us news and entertainment. We use it to get critical updates for home appliances. Some car manufacturers use broadband for telemetry and updates as well. Healthcare organizations are starting to leverage broadband connectivity to monitor patients. As COVID-19 rampantly rages across the globe, we are temporarily changing our lives such that our home and business connectivity is more important than ever. Securing the broadband experience must rise to the challenge of society’s reliance on connectivity.
Fortunately, our industry is designing future home environments that will be much more secure as we consider the synergy among gateways, modems, and access points with the devices they support and in particular when IoT are considered. Evolution is rapid and includes innovative new approaches, adaptation of fundamental standards and specifications including CableLabs DOCSIS®, and broader industry initiatives around Wi-Fi and IoT. This article will briefly touch on what cybersecurity on broadband is all about, review some ongoing initiatives, and discuss how readers can engage in bringing evolving capabilities to their own broadband companies.
Security is about the user experience
There’s a simpler reason. When a subscriber’s network is compromised, it’s a terrible experience. Whether it’s because of a security vulnerability of a cable modem or Wi-Fi access point, poor passwords for their configuration access to the cable modem or access, or lack of patches to their laptop, it means they may be dealing with stolen accounts, damaged IoT devices, embarrassing privacy breaches, or more. And fair or not, the subscriber is going to want to blame somebody. More often than not, the cable operator is blamed.
Cable Haunt
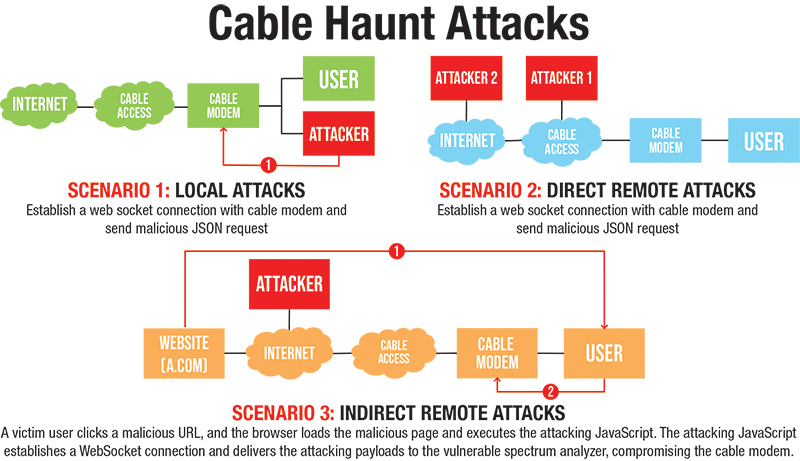
We’ve recently had a major security challenge for our industry. In January, it was released that some cable modems were vulnerable to a buffer overflow attack through the spectrum analyzer capability many modems support. Millions of devices were vulnerable. The attack could be realized from either or both the local home network or remote networks. As shown in the illustration, the most likely attack vector was luring a subscriber to a fake or compromised website through phishing. Malicious JavaScript would be loaded to the browser which, when executed by the browser, would attack the cable modem. There were many other variations. Readers can find more details at https://cablehaunt.com/.
Evolved solution
Cable Haunt illustrates the complexity of securing the subscriber experience nicely. In the attack vector discussed above, two things were done that resulted in compromise. First, a software vulnerability in a cable device (in this case a cable modem) provided an opportunity to the attacker. Second, the user fell victim to a phishing scam that allowed the attacker to find a modem to attack. Providing a great cable experience needs security that reaches deeper into the subscriber network.
CableLabs, and the industry at large, are working in a wide range of initiatives to improve security. We are evolving DOCSIS security. We are applying software defined networking (SDN) concepts to provide advanced infrastructures with user friendly security built in. And, we are working with Wi-Fi Alliance and the Open Connectivity Foundation to leverage standards-based capabilities for streamlined network onboarding and better IoT security. Here are further details about these on-going activities:
- Evolving DOCSIS security — DOCSIS security has not stood still over the past two decades. We’ve continually evolved. Now as DOCSIS 4.0 specifications are released, our access network security will see additional enhancements. These include support for better security of PKI keys, mutual authentication, and secure shell for more secure technician access. [1]
- CableLabs Micronets™ — Can we use security to dramatically improve our users’ broadband experience? Micronets [2]uses SDN and new features being provided by Wi-Fi Alliance to ensure more seamless device onboarding and security integration for customer premises. For example, we are using Wi-Fi CERTIFIED® Easy Connect to automate connecting devices over Wi-Fi. [3]
- Transparent Security — Securing the home is not always best achieved at the home. Sometimes, we need to do things deeper in the network. Transparent Security [4] leverages new silicon and application programming interface technology to execute new SDN capabilities at the hub, headend, or core. Enabled by the P4 Language Consortium [5], Transparent Security provides a framework to actually program the control plane of our routers and switches dynamically. An operator can specify exactly how a switch processes packets based on real time analysis of those packets leveraging high-performance ASIC or software-based infrastructure. This allows much more graceful and dynamic traffic filtering based on current and evolving threats.
- IoT Security — Device proliferation is dramatically growing, of course, as more and more sensors and actuators are deployed in our homes and businesses [6]. CableLabs has been working with its members through the Open Connectivity Foundation (OCF) [7] to specify strong security interfaces for consumer IoT. OCF also has significant work underway for industrial, medical, and automotive IoT. In addition to OCF CableLabs is engaged with other IoT standards organizations, including the Consumer Technology Association’s IoT security work group, R14WG1. SCTE is also working on IoT security on the Data Standards Subcommittee IoT Working Group [8]. SCTE also has some training available online for IoT [9].
Getting involved
Security is a continually evolving problem space. We are always coping with the new threats presented to us by very creative adversaries. It’s a real fight. There are lots of ways to help. CableLabs, SCTE, and NCTA all have activities on-going, even in these chaotic times, and can use your contributions. Reach out to your contacts at these organizations and ask, “Hey, how can I help on security?” They’ll get you introduced to the right people. Want to do something directly yourself? Some of the code from Micronets [10] and Transparent Security [4] is available. Take a peek, see how things work; contact information is available on the sites if you want to know more.
Conclusion
Future home and business environments are going to be dynamic and will support a range of interesting and valuable services. The experiences we enable will be transformative — and will include awesome security. Security is key to achieving our future experiences and will require strong synergy in security among modems, gateways, and access points. There are lots of initiatives underway — from DOCSIS security enhancements to new software defined networking approaches to enhanced security capabilities from groups like WFA and OCF. Members of the cable industry can easily get involved in these activities and make them even better.
References
[1] CableLabs DOCSIS® 4.0 Technology. https://www.cablelabs.com/technologies/docsis-4-0-technology
[2] CableLabs Micronets™. https://www.cablelabs.com/technologies/micronets
[3] Wi-Fi® Easy Connect. https://www.wi-fi.org/discover-wi-fi/wi-fi-easy-connect
[4] Transparent Security. https://github.com/cablelabs/transparent-security/wiki
[5] P4 Language Consortium. https://p4.org/
[6] A Vision for Secure IoT. https://www.cablelabs.com/insights/vision-secure-iot
[7] Open Connectivity Foundation. https://openconnectivity.org/
[8] SCTE IoT Working Group.
[9] SCTE IoT Fundamentals. https://www.scte.org/course-detail/iot-fundamentals-connecting-things-1/
[10] Micronets Github. https://cablelabs.github.io/micronets/

Steve Goeringer
Distinguished Security Technologist
CableLabs®
Steve Goeringer is a Distinguished Security Technologist at CableLabs. He is responsible for developing innovative security solutions for emerging technologies. Additionally, he is the security working group chairperson for the Center for Medical Interoperability where he has been building a trust framework and specifications for secure medical device interoperability. Steve creates new security approaches for cable architectures, innovations in integrating cryptography in cameras, blockchain solutions for cable and healthcare and new approaches to securing home networks
Shutterstock




